Contents of Post
Password Manager as a Security Solution
A password manager maybe a piece of software that remembers passwords, so you should not. By remembering one master password, all of your other passwords are securely stored for download as and after you need them.
Everyone should attempt to store their passwords securely. Together with two-factor authentication, it’s one of the simplest practices for locking valuable online accounts.
The password manager stores your credentials in a very database file. This encrypted file is protected by a master password or key file. This can be a confidential data management solution and personal data protection.
If you wish to access the identical database on another device, you may share it manually using cloud storage solutions. It is simple enough to try and do.
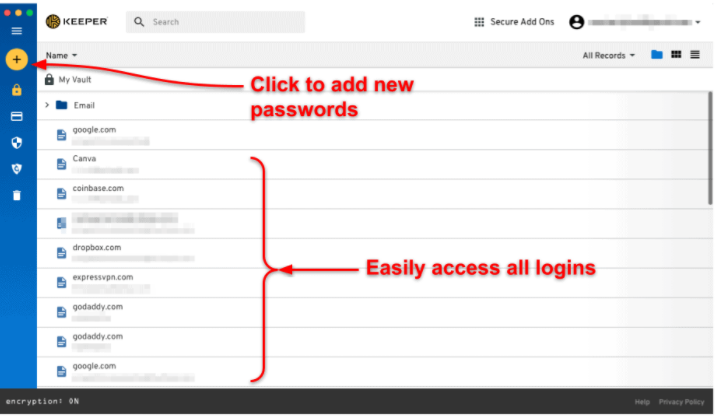
The password manager can store different passwords in folders or categories, with fields for information like usernames, passwords, and extra notes. Some clients include secure password generators, the flexibility to export the contents of your database to other formats, support for filling out web forms and plugins.
It allows you to store both confidential login information and secure notes within your account. Stay safe and secure using this app as an answer. Two-factor authentication should be enabled in your accounts whenever possible. This uses something you recognize (your password) and something you’ve got (usually your smartphone) to prove your identity.
Privacy on Social Networking Sites

The right to privacy is one of the fundamental human rights. the correct to be left alone implies the confidentiality of one’s data, unless there’s a transparent need for such data to be disclosed.
This issue requires a cautious approach in many areas. The matter of personal data protection is the subject of diverse research, discussions, and proposals of the final public further as scientists, governmental and non-governmental organizations.
The rationale for such good interest during this issue is predicated on the fact that the number of individuals who, more or less, voluntarily share information of various levels of confidentiality.
What worries me is that the information stored can remain there forever and in and of itself be available to different individuals and stakeholders and organizations. Around that, information, once released through the network, is currently transmitted through it and becomes globally available to everyone.
An additional problem, noticed by most analysts handling the matter protecting the privacy of knowledge on the net, is that users on their initiative voluntarily provide information about themselves (name and surname, addresses, telephone numbers, photographs, etc.) and at an identical time think a touch about the results of such actions.
In our opinion, social networking sites are the paradigm of today’s risky company. Since society is projected onto the web in its virtual form, it is understandable that by that analogy, the risks of the important are projected into the virtual world of the web Saint.
Social networking service providers also need, additionally to the will to amass profit, to think about people who indirectly bring them that profit, ie their users.
Unless personal data protection mechanisms are raised to a very secure level stay, users will start searching for other ways to network them. When users will understand that the private data they leave within the virtual space of the net is extremely realistic which the results of their abuse could also be reflected in their actual, not virtual profiles will then be much more cautious about who they will trust thereupon data on storage, and to whom not.
Internet and Media Literacy

The emergence of the web as a brand new electronic medium marked a turning point, not only in communication and availability of knowledge, has already contributed greatly to the change in the manner of life.
That the emergence of e-mail, online commerce and online banking, social networks, and therefore the like, on the one hand greatly facilitated way of life, but on the opposite hand has displayed new opportunities for privacy.
That’s why it’s important to emphasize that it’s Internet users must be educated about media literacy to understand one another better to protect. Privacy is often compromised in a very number of how – by disclosing personal information, such as names and surnames, residential addresses, phone numbers, checking account numbers, etc., and by publishing their photos and videos.
Although every internet user is potentially vulnerable, children are still the foremost vulnerable. That’s why media education and media education are important pedagogy to teach them from an early age. Self-protection and encryption methods data are a number of the privacy options.
Nowadays, it’s hard to imagine life without the web. We buy online, watch movies, and are attentive to music, communicating with friends, playing video games – the possibilities are virtually limitless.
But with all those positive aspects, they also occur negatively. one in all the foremost important and high is that the threat to privacy protection.
Change of Techniques and Technology

The emergence of the latest media is conditioned by changing technologies. Thus, additionally to the prevailing media, created the necessity for faster reporting, multimedia, and interactivity.
That’s the necessity satisfied with the arrival of the net. The net “networks” people around the world and provides instant flow and access to information and data, communication, and interaction, so it’s no wonder it’s becoming the first electronic medium.
However, its appearance was attended by many threats to the privacy of many users, which is why it was created and there are requests for privacy protection. To protect more, users need media and information literacy, and a variety of technologies are available within the types of personal data protection to be encrypted.
Besides, there is legislation on electronic communications, information security, and the protection of non-public data.
It is important to make the use of search engines and social networks as safe as possible. Do not forget that everything that is published through them can at some point become public, and thus available to everyone.

